Or the key fob you use to disarm your home security system.
Or even open the garage door.
The following GNU Radio flow graph could be used in conjunction with the RTL-SDR.
GNURadio makes it easy to filter out the jamming signal and obtain the authorized remote signal.
The signal obtained is the Nth rolling code, it is still valid because the receiver has not yet received the Nth rolling code. Therefore the adversary can replay the signal at a later time and unlock the car. But how does one replay the signal on the cheap?
The system that was constructed looks as follows from a high level.
The signal in this case was ASK (Amplitude Shift Keying) encoded data which was decoded using GNU Radio's "AM Demod" block as follows.
The demodulated signal was then played back through the audio interface of the computer.
The signal was then fed into a LM386 op amp to bring the signal from line level (~1V), up to TTL (~3V). The TTL signal was then fed into an ASK RF module operating at the same frequency as the authorized remote. The schematic for the constructed circuit follows.
And the final product was soldered onto some prototyping board.
The board here is powered by USB, and has a switch on the back right portion of the board. This switch allows you to put the board in either "Jamming" mode, or "Signal Replay" mode. In "Jamming" mode, the RF module will continuously transmit bogus data at the carrier frequency. In "Signal Replay" mode, it will transmit the data provided through the audio jack as an ASK encoded signal at the carrier frequency. A 315 MHz ASK module was used, but this module is inexpensive and could easily be swapped out for say a 400 MHz FSK module. A list of the parts used in it's constructed follows.
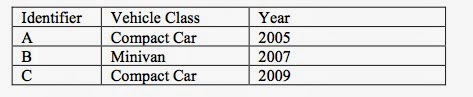
Does this system actually work? Frighteningly, yes it does. I was able to test this attack against two economy cars and one van, all of which use rolling code security.
In a rolling code garage door system, imagine the following
sequence of events. The victim presses the button on the RF
remote to initiate the closing of the garage door. The
adversary jams and intercepts the signal. The garage door
therefore does not close. The victim presses the button on the
RF remote again. The adversary jams and intercepts the signal
again, but then replays the first signal he/she intercepted. The
garage door closes, and the victim leaves the area assuming
that their garage door is secure. The adversary then replays the
second signal he/she intercepted and the garage door opens
again.











Cool :D
ReplyDeleteToo Curious For My Own Good: Jam Intercept And Replay Attack Against Rolling Code Key Fob Entry Systems Using Rtl-Sdr >>>>> Download Now
Delete>>>>> Download Full
Too Curious For My Own Good: Jam Intercept And Replay Attack Against Rolling Code Key Fob Entry Systems Using Rtl-Sdr >>>>> Download LINK
>>>>> Download Now
Too Curious For My Own Good: Jam Intercept And Replay Attack Against Rolling Code Key Fob Entry Systems Using Rtl-Sdr >>>>> Download Full
>>>>> Download LINK 0Y
Were you able to actually test the attack you describe against the garage door (on the vehicles)? Such attacks are fairly well known and easily defeated by requiring a sequence number as part of the protocol, thus transmitting keys out of order won't work. A possible attack would be to jam both attempts to close the garage door, except after the second attempt replay the first code. So the user sees the door close, but the second code remains valid.
ReplyDeleteThat type of attack is also well known and defeated by having a clock involved on both ends. But such a countermeasure would be difficult to implement on a cheap fob where the battery needs to last a long time.
I was unable to test the attack against my garage door, the particular model I have operates based on phase shift keying at 315 MHz and I was unable to find a cheap module that does PSK @ 315 MHz. I could construct one, however I wanted to keep the build to be a simple proof of concept. The price of a SDR is falling and eventually there will be no need for custom hardware for replay. It works on the three vehicles as they operate at either 315 MHz or 434 MHz with ASK.
DeleteI agree, manufacturers are just looking to keep everything cheap and simple. The bidirectional PKES keyfobs have their own issues, and I wonder sometimes if they are even a step forward.
Hi, really cool hack. There's one point that's not quite clear regarding the last paragraph. If the key fob has separate lock and unlock button then the ability to jam two commands, to be able to repeat the second one later seems useless. You can lock again something that's been already locked.
ReplyDeleteTrue, however if you jam for long enough, you will eventually be able to collect an unlock signal when the victim gets frustrated.
DeleteHi really interesting work. What if you jam at the same frequency as the fob? Probably you will not be able to filter out the jam signal, how would you solve this?
ReplyDeleteI was thinking, if you would use a patron for you jam signal, like a pulse every 25% of the key length, you could minimize the amount of possible codes to a hand full. Because you would knockover only a few bits, that can be quest afterwards. In this way cheap electronics can be used. What do you think about this?
You can technically jam at the same frequency of the fob. The resultant signal will just be the superposition of the two signals. Since you know exactly what the jamming signal looks like, you can then subtract the jamming signal to obtain the authorized remote signal.
DeleteThis of course is overkill because I can jam at say 315.15 MHz, while the remote is transmitting at 315.16 MHz, and still be able to filter by frequency and obtain the original signal.
This would work, and in fact my first revision of the hardware was capable of doing this. The issue is that it requires you to have knowledge of what the protocol is. Protocol information is not hard to find online, however it adds a significant amount of time to the whole process. That is why with this revision I moved to more general hardware that would work for a larger class of systems.
Whats the value on the ceramic capacitor?
ReplyDeleteAnd what i understand this is a manual process and it require you to know the frequens of the key? Can it be written to a automatic python software?
In retrospect, you can get away without using the ceramic capacitor. I do not own an oscilloscope, so that ceramic capacitor was in there from the testing stages when I would hook up a speaker and test the circuit by listening to the output.
DeleteYes, this requires you to more or less know the frequency of the key. There are only a handful of frequencies that these key fobs operate at though.
Yes. The first version of the system was purely digital and automatically picked up on when someone pressed their key fob. A few GNURadio blocks had to be written to make this work though. It is beyond the abilities of the average joe.
Can you share your flow graph files? Thanks!
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteThis comment has been removed by the author.
DeleteHello Spencer,
ReplyDeleteI have been searching for the right info to implement a proof of concept on decoding the key fob signals and possibly reverse engineer the encryption key.
Finally found the right place...
I am new to SDRs...
Could you please guide me to the required software resources to work with the DSR -RTL for signal capture, demodulation and decoding
many thanks
Hey,
DeleteEverything software side was done in GNURadio, here is the best place to start: http://gnuradio.org/redmine/projects/gnuradio/wiki
If you are looking for more information on the specifics of attacking these systems, you can check out:
http://people.scs.carleton.ca/~barbeau/Honours/Spencer_Whyte.pdf
can you upload a video tutorial of how to program the components?
ReplyDeleteHey why don't i just build u the damn thing, for free.
DeleteI was trying to do Jam intercept and replay according to your instructions. In the beginning it went very well, I got the signal, made Raw_Jammed file with all data. When next making Raw_De-jammed file, after many tries GNU Radio still gives me this - Firdes check failed.
ReplyDeleteCould you kindly help me with this? (I am using HackRF, GNU Radio 3.7 and Linux Ubuntu 14.04.).
Here is my output:
File "/home/..../top_block.py", line 55, in __init__
1, samp_rate, 500, 22000, 250, firdes.WIN_HAMMING, 6.76))
File "/home/linux/target/lib/python2.7/dist-packages/gnuradio/filter/filter_swig.py", line 155, in band_pass
return _filter_swig.firdes_band_pass(*args, **kwargs)
RuntimeError: firdes check failed: 0 < fb <= sampling_freq / 2
Please help me to look into this, what should be done to fix this Firdes error?
BR,
Iluta
My mail: iluta2009@gmail.com
The error says that your upper frequency parameter to the filter does not make sense with the sample rate you are using.
DeleteWhat is the sample rate on your graph?
What is the upper frequency on the filter block you are using?
Thank you very much for your response! For Nth Rolling code flowgraph I'm using:
ReplyDeleteThrottle - Sample rate 40e3
Band Pass Filter - Sample rate 40 mhz, high freq 22e3, low 500
Upss..I see a mistake - Filter upper frequency (22e3), cannot be lower than sample rate (40e3)...? Or there is anything else I cannot see?
(Forgive my asking, since I'm not at all IT or radio specialist). All self learned and just recently. :D
So if you look at the last line of the error, it says that there is a problem with the following check:
Delete0 < fb <= sampling_freq / 2
Now if you substitute the values that you provided...
0 < 22e3 <= 40e3 / 2
0 < 22e3 <= 20e3
You will notice that the inequality above does not hold. Therefore the check fails. Try increasing your sample rate on the throttle, or decrease the upper limit on your band pass filter to something less than 20e3.
Hopefully I am interpreting your error message correctly. Let me know how it goes!
This comment has been removed by the author.
ReplyDeleteYes, it works starting up with the lowest Throttle sample rate 44e3, which is logical as sample rate freq 44 / 2 = 22. I even didn' t touch filter limit, didn' t see need for it, since raising them accordingly to sample rate will be OK. Now:
ReplyDelete1. Raw Dejammed file FFT plot shows these very extremely low noises -70 to -100 db? Was it all I got when I picked up in my Raw Jammed file and got as output in Dejammed as well, though I tuned in to 315 mhz initially.
2. Of course, AM Demod My Attempt file FFT plot shows noise -60 to -130 db.
Where went my 315 mhz signal...? (I had a good reception, and before checked signal on Constellation plot, it was quite ok).
I added to Get Remote file both Throttle and Constellation sink, and I made my key fob at 868 mhz visible and written to a file. (throttle sample rate 1e6).
ReplyDeleteThen made it as Dejammed File (Throttle rate 44k).
Then Raw Dejammed to AM Demod file (Throttle rate 100e3).
Could this be that failure to get a decent signal back could be because of:
1. Different Throttle sample rates.
2. Making wav file in the end, and not deciphering to Quadrature and Bits?
Or I might as well missed something.
Hi there, i was trying to replicate your prototype breadboard but noticed that the 315mhz ask transmitter is attached to a chip on the board and the ones you can buy online only come with pins?? i can see the lm386 and this is listed in your parts used. am i missing something? could you let me know what the ask transmitter is attached to??
ReplyDeletemany thanks for your help
As you can see in the photo with the protoboard, the ASK transmitter appears to be directly connected to the LM386, however you cant actually see the connections that are on the bottom side of the protoboard.
DeleteMy advice would be to follow the schematic shown above the protoboard.
The ASK transmitter won't come with the LM386 attached, you will have to buy it separately and connect it yourself using either breadboard or some protoboard.
Let me know if you have any more questions.
http://ctstechnologys.com/2015-hand-held-rolling-codes-jammers.html
ReplyDelete2015 Hand held Rolling Codes Jammers
Hello !
ReplyDeleteI made the circuit diagram and gnuradio schemes of your project....!! The "jamming mode" worcks but in "Signal Replay" the signal who was recorded , dejammed , demodulated and out to sound card - jack - LM386 - appears to be very weak, on the SDR can not be detected, neither audio nor frequency. I use a 433Mhz ASK Transmitter and i update all gnuradio scheme with 433Mhz.If i listen the .wav file the signal it 's there ... It is there on registration and can be seen and heard perfectly ( both audio and frequency ) on SDR.
On first graph i allso have a "invalid sample rate 4000Mhz"....
Need some help !!
does your module unlock cars?
DeleteHello,
ReplyDeleteGreat Work !
In my Eyes, Guys Like you are realy important for Science and progress.
I follow a few of your posts a long time but never post/ask something.I just like your skill/posts (it could be more :) but its okay)and until now, it was enough for me to only read from you.
But this time...Maybe, if you could spend me some of your worthy time, i would happy about asking you something.
It would be awesome if you could post one or two more Pictures. I would be happy to see the "back" (otherside). I dont Check how i input the audio signal.And your Schema doesnt show it. (Where goes the signal and gnd of the audio cable?)
Whats that in the left corner (down) ?
Is that the 3,5 mm audio input ?
Why is the cable this big, or i understand something wrong, and you dont become the "input signal " from the audio cable ? And thats something other ?
Sry my english is bad as my hardware skills. ^^
It would help me this much, if you can post or send me some Pictures or a detailed Schema (maybe for low skilled guys Like me), im good in software, programming but Hardware...not really. I want to get better skills and it would be a honor if you could help me a bit, with photos or/and Schema.
Greetings from Europe,
Reegards
Tim
I did try with HackRf but I had issues.
ReplyDeletedid you unlock cars with hackrf?
DeleteThis comment has been removed by the author.
ReplyDeleteNobody helps here !!!
ReplyDeletecan anybody help me in this issue?
ReplyDelete??
ReplyDeletecan somebody make such device?
ReplyDeletewhat if its are 433mhz signal. do you have are mail where i can contact you on. i have some question?
ReplyDeleteDid you write this to me?
DeleteHi, I did try with hackrf , but dont works , I has dificulf with filter. Please if someone can help me , email me .
ReplyDeleteHOLA AMIGO ESTOY CON EL MISMO PROBLEMA,ME PUEDES AYUDAR??
ReplyDeleteIs there any videos or photos to refer to?
ReplyDeletecan I use hackrf instead of rtl sdr and this folowgraph to do the same operations as published here?
ReplyDeleteHow can you determine the modulation type? I can not find a way to determine ASK,PSK or FSK modulations just by looking the signals caught
ReplyDeletehey there... I want to ask a question that is a bit of subject but i figured if anyone would know, you could answer my question. can i jam any signal(radio communication) ranging from the HF,VHF and UHF using the hackrf one, witch does operate on 1mhz to 6ghz?
ReplyDeleteplease,if you can help me you will be doing me a big solid. i just want to make sure of my facts before spending so much money on something i thought i could do a specific thing with and then turns out i cant!
Its illegal to jam any freq....
Deletehey there... I want to ask a question that is a bit of subject but i figured if anyone would know, you could answer my question. can i jam any signal(radio communication) ranging from the HF,VHF and UHF using the hackrf one, witch does operate on 1mhz to 6ghz?
ReplyDeleteplease,if you can help me you will be doing me a big solid. i just want to make sure of my facts before spending so much money on something i thought i could do a specific thing with and then turns out i cant!
Hi, Very interesting project. Maybe you can help !
ReplyDeletei try to raw record my aircooling system at home. Trying to record "ON" and "OFF" RF434 signal.
Then be able to replay it with raspberry and arduino
At the moment i am able to record with gqrx , open in audacity. But i am stuck when i want to replay
can you help me ?
regards
? Have you tried URH? Does the aircon system use rolling codes or fixed?
DeleteA car alarm system is an electronic device installed in a vehicle in an attempt to discourage theft of the like OEM alarms, aftermarket systems are usually armed and disarmed via remote.
ReplyDeletewww.timensound.com
gopainlesswiring.com years of experience with custom wire harness manufacturing services for a range of industries
ReplyDeletefantastic project just got a hackrf recentley can i use my iphone with the hackrf ?
ReplyDeletedarshana industries dealers in bangalore
ReplyDeletedarshana industries
I have read your blog with great interest.
ReplyDeleteIf I use GNURadio and HackRF One, can I get the same results without changing the flow graph and without fabricating the board?
This comment has been removed by the author.
ReplyDeletet's now 2021. Are there any garage door remotes manufacturers that learned from you and that implemented counter measures?
ReplyDeleteEspecially now doors closes automatically after a car passing by, a 'save two presses, resend first and keep second' scheme would work. I don't think those simple garage door remotes have time in the message (how to sync that?).
I have seen a French and a Spanish remote that have a 'car is in the garage' logging (anti pass back). That would help, wouldn't it?
ReplyDeleteA roman blinds does provide an effective and solid kind of pattern fabrics which is suitable for
the living rooms and bedrooms respectively. A way of decorating your home windows with defined
size and custom size from the number one service in Melbourne in the name of Australian Window
covering service.
roman blinds
Won't beat about the bush...its just what every1 want too know.
ReplyDeleteWHERE CAN I BUY 1 FROM ?????
Too Curious For My Own Good: Jam Intercept And Replay Attack Against Rolling Code Key Fob Entry Systems Using Rtl-Sdr >>>>> Download Now
ReplyDelete>>>>> Download Full
Too Curious For My Own Good: Jam Intercept And Replay Attack Against Rolling Code Key Fob Entry Systems Using Rtl-Sdr >>>>> Download LINK
>>>>> Download Now
Too Curious For My Own Good: Jam Intercept And Replay Attack Against Rolling Code Key Fob Entry Systems Using Rtl-Sdr >>>>> Download Full
>>>>> Download LINK 4y